Hi Mik,
There is an attempt at a network attack. Dero’s network is fighting back fairly hard and when we have more information I will let you know. Electroneum (ETN) had their network thoroughly pummeled earlier, as did Sumo.
For now, Dero is faring significantly better than the others but we will have to see how things play out.
Thanks for reply ! Is it worth to continue mining or the current shares are lost ?
If you’re on the official pool you should be okay 
Thanks a lot ! … 
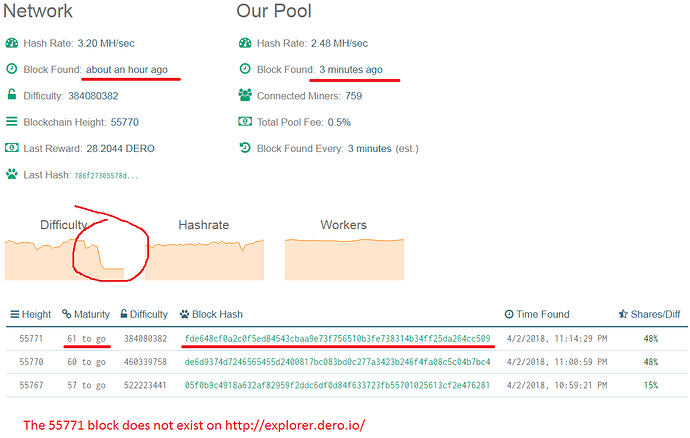
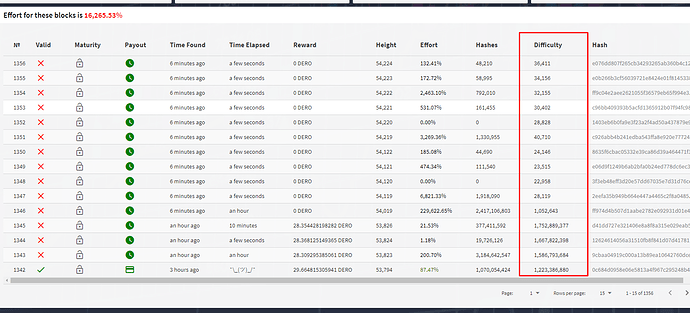
Just for records.
Diff vulnerability that is affecting many CryptoNote/other blockchains where attacker/tester mines numerous blocks in less time with very low diffs. Golang code was made resistant against such attacks but not C daemon. We were in test phase and mid of migration when attacks started, So we shifted to Golang alpha version completely on that date technically, dropping support of C version completely.
For the records:
Block #9900 - Attacked on Christmas(2017) - patch is released 24 hours later and vulnerability is closed.
Block #42100 - Attacked and unexpected series of soft forks - patch is released 48 hours later with many vulnerabilities closed.
Block #53600 - Attacked - sudden early transition to golang which had significant security upgrades. This stops the attack but was an unexpected early switch to the new mainnet.
Block #57000 - A very public call out to attackers including those hitting all existing CryptoNote network, XVG, bitcoin gold, etc.
Block #68600 - Attacked & unexpected hard fork - attack from people with advanced cryptography knowledge. A 70% hashpower attack results in 6-8% of mined blocks going to the attackers with a dozen orphans or so, and no network damage.
Block #82800 - Attacked ~550 MH/s to 1.95 GH/s - 70% attack with zero issues, and the public does not notice, but it is well recorded in the blockchain history.